![]() I had posted how to use Wireshark to capture network port usage while back. I poked Wireshark some more and it is probably a bit too advanced for my occasional use.
I had posted how to use Wireshark to capture network port usage while back. I poked Wireshark some more and it is probably a bit too advanced for my occasional use.
So when I caught mention of SmartSniff packet capture utility from Nirsoft I was very interested if it can deliver simpler experience for network traffic capture.
What it does
SmartSniff uses one of three methods to capture network traffic:
- raw sockets (described as unreliable, worked fine for me);
- WinPcap driver;
- Miscrosoft Network Monitor driver.
For any of the options result is the same – packets passing through network adapter are captured and logged.
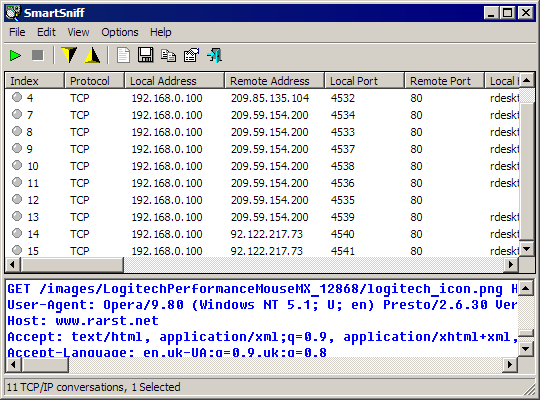
Top part of interface is usual for Nirsoft multi-column view with data, lower pane shows internals of selected packets, which can be displayed in automatic mode (default), text, HEX or list of URLs (if applicable).
Strong features
The app is easy to use and capture process is easy to control. Columns display a lot of information in structured way (as usual).
I liked most that:
- it can work in statistics only mode, sometimes precise connection stats are more interesting then specifics;
- filter rules are easy to write and apply (something I struggled with in WireShark).
Downsides
SmartSniff can display (if enabled in options) which executable connection belongs to. This is really useful but there is major feature missing that filters cannot include/exclude by process name. Such option would make it much more useful in many scenarios.
Overall
Not as feature packed as professional software, but simple, tiny and portable sniffer that makes great addition to tech’s toolkit.
Home&download http://www.nirsoft.net/utils/smsniff.html
Dotan Cohen #
Rarst #