![]() This week I had bit of a tricky things to accomplish. I needed precise log of network ports used during interaction of two computers. There is no shortage of simple connection monitors (like TCPView) but they aren’t precise enough for quick connections or good enough at logging.
This week I had bit of a tricky things to accomplish. I needed precise log of network ports used during interaction of two computers. There is no shortage of simple connection monitors (like TCPView) but they aren’t precise enough for quick connections or good enough at logging.
Wireshark (previously Ethereal) is rather known network packets analyzer which I thought is bound to have something fitting for the task.
What it does
Wireshark is packet analyzer that makes use of WinPcap driver to capture and analyze all (or subset of) network traffic. It is low-level tool with many uses, I only cover small slice of functionality in this post.
Installation
I went for version packaged in PortableApps format. It still needs WinPcap installed and for portable version it automates install/uninstall prompts for it when you run or close Wireshark.
Other than that works as any regular PortableApps software.
Capture
Click Capture Options for live capture settings dialog. You need to choose correct interface (network card) to run capture on.
To filter down to interaction with specific computer set filter, for example I used address of my notebook in home LAN:
host 192.168.0.101
Capture can be stopped manually or you can set limits how long to run or how much to capture. After pressing Start live capture will immediately run until stopped or reached limit.
Analyze
Raw packets don’t make much sense (well, to me). Luckily there are number of options to dumb it down for specific tasks. To get port usage that would be Statistics > IP Destinations > Create Stat
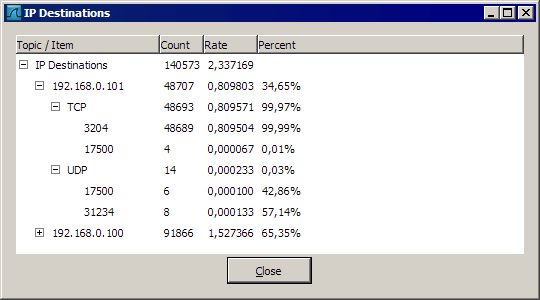
wireshark_ports
This creates precise protocol and port usage of captured traffic, split by IPs coming from to target ports. There are also percentages that help distinguish bulk of traffic from occasional packets.
Overall
Wireshark is powerful tool and may seem overly complex at first sight. But there is number of functions convenient and easy enough to make use of it even without deep knowledge of network specifics.
Home http://www.wireshark.org/
Download http://www.wireshark.org/download.html