![]() Windows has interesting registry key called Image File Execution Options. It is rarely useful to users but is total bliss for viruses. Worst part – modifications viruses make there often cripple system for good even after virus itself is removed.
Windows has interesting registry key called Image File Execution Options. It is rarely useful to users but is total bliss for viruses. Worst part – modifications viruses make there often cripple system for good even after virus itself is removed.
So if system behaves strangely after virus attack was cleaned then remaining harmful registry entries must be destroyed.
What it does
Registry key provides perfectly legitimate function – attaching debuggers to executable files. In human language – it allows to create entries that say if application A is launched then start application B instead.
How viruses use it
- Attach to common system executables (like explorer.exe) to secure running virus always and in a manner harder to detect than common autorun entries. When virus is removed this may prevent system files from running at all.
- Prevent antivirus software from running by attaching executables that may not even exist. If antivirus utility can’t start it is worth to try renaming its executable file.
Cleanup
Manual registry editing is always an option but far from comfortable. Much easier is using Autoruns which has Image Hijacks tab.
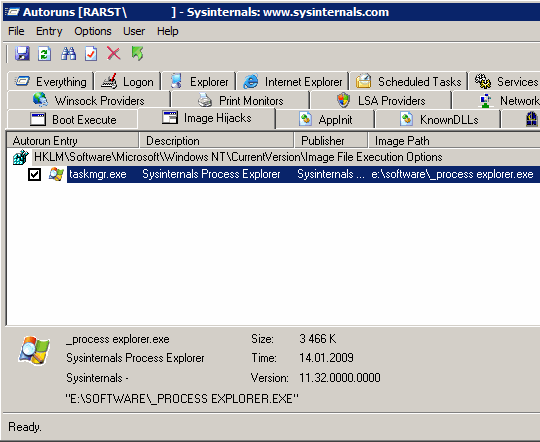
On screenshot there is example how Process Explorer replaces Windows task manager. If there are entries here – it is often sign of virus infection. Right-click > Delete (or Ctrl+D or Del) to remove entries, right-click > Jump to… to open entry in registry editor..
Lyndi #
Rarst #
TechZoomIn #
Rarst #
MK #
Rarst #
TechZoomIn #
Madmouse Blog #
Rarst #
Madmouse Blog #
Rarst #
Nihar #
Altiris_Grunt #
Rarst #
Altiris_Grunt #
RegScanner – search app for Windows registry | Rarst.net #
RegFromApp – simple registry monitor | Rarst.net #
Marvin #
Rarst #
Marvin #
Rarst #
Marvin #
Rarst #
Altiris_Grunt #
Rarst #
Jonny Vee #